 Aside from a couple of “conceptual” examples shown at conferences here and there, the only real piece of malware on the Mac that’s made it “into the wild” is the now infamous MAC Defender and its variants….one of which, MacGuard, has recently made headlines.
Aside from a couple of “conceptual” examples shown at conferences here and there, the only real piece of malware on the Mac that’s made it “into the wild” is the now infamous MAC Defender and its variants….one of which, MacGuard, has recently made headlines.
Naturally, the MacGuard topic has hit all the major tech news sites, igniting yet another round of “Mac vs. Windows” flame wars. Ironically, all this attention is probably helping the malware’s progress; I’ll go into m0re detail on that in just a moment. First, I’d like to clear something up.
MAC Defender and its variants are not viruses!
To date, there are NO actual “viruses” out there for OS X. Like its biological namesake, a computer virus can be transmitted simply through exposure. If, however, you are immunized against it—either through natural resistance or by getting immunized— then you don’t get sick.
It’s the same way with computers. Web sites, emails and the like can be “infected” with a particular virus, opening up your computer to infection as well. If you have a Windows box, you’d better be up-to-date on your antivirus software (the “flu shot”) or your computer is going to contract that same virus. Macs, on the other hand, use a completely different code base, which is highly resistant to casual infection. They’re like those kids from that one episode of Star Trek: The Next Generation that had enhanced immune systems, except your Mac isn’t likely to prematurely age others to death…
In short: there are no true “viruses” for the Mac.
So what are MAC Defender and its variants?
MAC Defender and its variants are “Trojan horses,” rather than true “viruses.” They owe more to “social engineering” than to any technological prowess. The only way MAC Defender and/or its variants can get on your system is if you choose to install it. The trick for the malware authors is to actually get the user to do so.
So how do they do that? Trickery.
And their target audience is made up of four groups:
- The Conditioned. As the Mac platform has grown, there have been a lot of converts from the Windows side of things who are used to constant virus threats and having to keep antivirus software updated; for them, virus alerts and responses are nearly reflexive.
- The Fearful. Users whose exposure to computer related topics is primarily gleaned from mainstream news—again, primarily Windows-centric; when they hear there’s a “virus” out, they grow fearful that something terrible is going to happen to their computer.
- The Uninformed. Those that use (and think of) their Mac as an appliance and pay no attention to computer related topics. So if a pop-up appears, they just click it like they would a system or other software update.
- The Clickers. Those who are simply careless in what they install and from where; a window pops up and they click “OK” without bothering to look at what it says.
The scammers behind these pieces of malware prey on the aforementioned users’ naiveté and/or laxity regarding their systems. They set up their site with information “of interest” to potential victims (often by “poisoning” a Google search by including popular keywords), and code it so that once they’re on the page for a certain amount of time, a window pops up that looks a lot like a Finder window, claiming that the computer is “infected.”
At this point, users usually do one of two things; they either close the browser window and move on, or they go all “Chicken Little” and start downloading utilities willy-nilly.
And, of course, there just so happens to be a “fix” offered right there in the pop-up window, ready to be downloaded, installed and opened by the user.
If that happens, the user’s Mac does have malware installed.
As malware will do, it then starts causing the computer to open sites (often of an “adult” nature) at random times and spouts out “warnings” that your computer is “infected.” Of course, conveniently enough, that “anti-virus” program has a fix; they just need a credit card number…
This isn’t as bad as you think…
Apple has wisely avoided giving a lot of press to this issue. If they came out like the rest of the press is, then they’d be just spreading the panic and, ironically, cause more instances of this software being installed (“Oh, I must have that virus Apple was talking about. Oh goody, these guys have a solution…”).
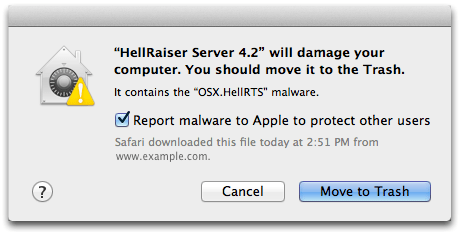
However, that doesn’t mean Apple isn’t doing anything about it. Yesterday, there was a software patch released for OS X 10.6 that updates XProtect (an integrated part of 10.6) to check for MAC Defender, remove it if you’ve got it already, and warn you if you try and open a downloaded version. Unfortunately, less than eight hours after Apple released this patch, newer variants that circumvent this detector, such as MacGuard, have been found. However, XProtect itself has been updated to check for new malware definitions daily; as soon as a new definition is put out, you’ll get the update. It really is just a matter of time on that one, and Apple certainly has the potential to kick those definitions out faster, especially now that it’s focusing on them.
In the meantime, rather than relying on your computer to tell you a file is potentially dangerous, you just need to use a little common sense to protect yourself from malware like this.
Don’t lose your head; use it.
If you’re surfing along and a window pops up saying you have a virus and/or you should install some program or another, ask yourself these four simple questions:
- Do I have antivirus software installed on my computer already and if so, is that what the warning looks like?
- Has my computer been exhibiting unusual behavior previous to this pop-up?
- Is this software being downloaded from a company I’ve heard of before and trust?
- If the software installer is automatically running, did I intentionally launch that program from the Finder?
If you answer “No” to any of these questions, then do not install the software!
This malware, like many Trojan Horses, relies on the end user being fearful and/or misinformed about Mac malware in order to ultimately profit from its sole purpose of getting that credit card payment. Don’t give them anything to work with.
Keep up on your Mac news from reliable sources like MacFixit, AppleInsider, The Unofficial Apple Weblog, and even here at the OWC Blog. Learn about what’s going on with the OS and what potential things to look out for.
And, on the off-chance that you do come across one of these pieces of malware, just take a hint from the late Douglas Adams and “DON’T PANIC” Keeping your head and thinking things through will help you a lot more than that offer for software that just happened to pop up…














I’m having a hell of a time of people accessing my computer either though my phone company router or remote apps. I’m new to Mac but is their anything I can do to keep old men from watching what I do on my computer all day? The digital harassment has been about 3 months but the overall coughing and whistling freaks who moved in this town has been about 12 years. Is there such a thing as privacy on any network or does Israel watch everyone jerk offs from their living room?
MacKeeper has some of the makings of being a Trojan Horse or similarity to MacDefender. It requires an account to be made for ‘Theft Protection’ and ‘Geek access’ whether you want those features or not. If not a Trojan Horse, it is very big brother considering the ability to track your machine if stolen . . . questions what else it is able to do behind the scenes.
I already knew all this. the reason I am here on your page is because while i was surfing, a window popped up (WINDOWS malware alert. it said my PC was infected and I needed their WINDOWS virus software to get rid of the problem) now, obviously this is malware, as I use a Macbook Pro, however, the problem lies with the fact that it promptly popped open my downloads folder, and downloaded it’s self. I did a force quit on safari, and deleted the file in finder, and cleared the downloads folder, and emptied trash. I then reset safari, and cut off airport. I did a quick scan with virusBarrier Express (free from the appstore) it said no threats found, and then turned airport back on. after that, i jumped around a couple different sites (Facebook, twitter, youtube, etc) and when I opened a new tab and typed google, i got, instead of google, another pop up saying i have malware and such, but this time it didn’t look the same, nor did it download it’s self. i decided to retrace my steps and went back to the page where I had seen the first pop up, and ran the Ip, i discovered it was on a proxy, and now it was the same pop up as the second one (they were different remember). so, I’m not sure if I have malware or not, but being that it visibly downloaded it’s self, i’m fairly certain i do, even though a scan did not see it. the file only downloaded, i did not execute it, but i was reading that a few known Mac Malware programs can auto install without root, or admin privileges. i also do not see anything funny in my activity monitor, but I also read that they can be hidden from that, from finder, and from force Quit. after I submit this, I am going to force terminal to reveal hidden files, but any advice would be greatly welcomed.
Chris, Good article.
Personally, I find the issue in all this mess to be with web browsers that make it too easy to confuse the novice user.
Life would be much easier if javascript/flash were prevented from doing anything outside the browser window. No popups, no new windows. None of those “enhanced” features that are so easily used to make for a bad user experience.
And as a pro user, all those browser features only make for a SLOWER user interface.
Great article, and well written. I had the MacDefender window pop up while visiting a travel site; didn’t install it, but it was my first in-person experience with Mac malware. I immediately notified all my (possibly less-experienced) Mac friends with an email; your article will be a good resource to share. Thanks!
“If that happens, the user’s Mac does have malware installed.”
Given the flow of that sentence from the previous, some might read that as saying, “If you see that pop-up, your Mad DOES have malware installed.”
Better to say, “If the user DOES download and install that alleged “fix” then there WILL be malware installed.”
As the owner of a Mac based law firm, this was a comforting and informative blog. While I’ve been a Mac user for 8 years, and “know better”, a few in our firm come from the fear based Windows world and might have been tricked, more likely on their home Mac since I’m at the office to address questions they have regarding popups on their work Mac.
Thanks, I continue to enjoy your products and services.
Glad to hear it Mark…on all accounts!
Sound advice backed up by simple truths. Thanx!!! Good Job