 Tomorrow, January 28, is Data Privacy Day. This day is set aside to “raise awareness and promote privacy and data protection best practices,” and earlier in the week we showed you how to use FileVault on Mac to encrypt your data automatically. Today we’re looking at how Virtual Private Networks (VPNs) work to keep data safe while connected to the Internet.
Tomorrow, January 28, is Data Privacy Day. This day is set aside to “raise awareness and promote privacy and data protection best practices,” and earlier in the week we showed you how to use FileVault on Mac to encrypt your data automatically. Today we’re looking at how Virtual Private Networks (VPNs) work to keep data safe while connected to the Internet.
What’s a VPN?
Simply stated, a Virtual Private Network (VPN) secures your computer’s internet connection by making sure that all of the data you send and receive is encrypted. VPNs are often put into place by companies to connect data centers and offices that aren’t on the same physical network, but for individuals they’re used to secure communications on untrusted public networks.
Many corporations use VPNs to give offsite workers a secure connection to a local area network (LAN) in an office facility. VPNs are generally enabled by launching a VPN client application on the worker’s computer, then logging in with credentials and/or biometric methods like Touch ID. The computer — and it makes no difference if it’s an iPhone or a Mac Pro — then exchanges trusted digital keys with the remote server. As soon as both computers verify each other as authentic, all communications between them through the unsecured Internet are encrypted and secure from any eavesdropping.
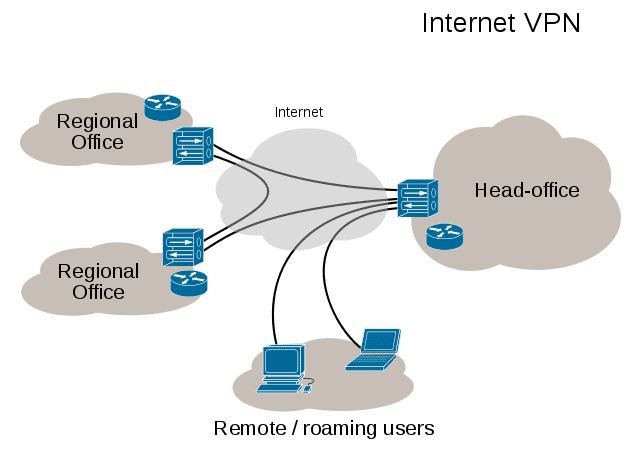
VPNs take advantage of tunneling, a way of encapsulating Internet Protocol (IP) packets within other packet formats so that the original data is “hidden” from anyone attempting to read those packets. While the behind-the-scenes data manipulation involved in tunneling is beyond the scope of this post, the analogy of a tunnel between two end points is perfect for visualizing how your data travels from your device to a remote server without interference from outside.
Another common use of VPNs is to allow access to websites or services that are geographically limited. For example, video streaming services are often limited to specific countries, which makes it difficult to watch favorite shows while traveling. By using a VPN to connect to a streaming server in a remote country, the server “sees” the connecting device as being in the same country.
Who Uses VPNs?
VPNs are used by a lot of people. As mentioned in the first section of this post, companies want to make sure that employees can have access to resources on the corporate network while working from home or traveling. Workers are usually provided with free VPN service and client software to connect to the office network, and are generally given strict instructions to use the VPN when on any network outside of the office.
Some people keep their privacy and data security in mind all the time, something that the organizers of Data Privacy Day would like to see more of. These people often use VPN services to keep all of their communications encrypted regardless of what network they’re on.
Travelers who want to keep up with local or national news from a favorite source that might be blocked in another country like to use VPNs to bypass location-restricted streaming services. This is also a way to try out web services or apps that are enticing but are limited to a specific region.
How Do I Select a VPN?
Corporate and government users, as well as students connecting to a campus network, usually have their VPN selected for them. For the rest of us, there are a number of different decisions to be made to find a workable VPN. Feature set, location of servers, the connectivity protocols used, and price are all important factors to take into account while making a decision.
Protocol – VPN providers use a lot of different terms to describe the protocols used to encrypt and secure your communications. SSL/TLS (otherwise referred to as OpenVPN), IPSec, L2TP, and PPTP are all acronyms describing a specific protocol. Most corporate VPNs use either IPSec or SSL clients, while PPTP has fallen out of favor with many security experts due to well-known vulnerabilities.
Logging – While the entire idea behind VPNs is to keep your data secure, some VPN providers keep logs of your activities while you’re connected. Corporate/government or school users are almost certainly having their data logged, as that provides IT departments with a way to ensure that no one is making illegal use of their network. For those who are concerned about personal privacy, make sure that your VPN provider does not log your activities.
Location – Potential VPN users should also consider the corporate location and the exit locations (countries in which your communications “emerge from the tunnel”) of the services. This is especially important for those who want to get around location restrictions for streaming TV; if you wish to watch live TV in France, for example, make sure that the service has servers in that country. Make sure that a VPN has servers in multiple locations while looking for a potential service.
Devices – If you’re going to use a VPN on your Mac, you’ll almost certainly want to make sure that your other devices are able to use the service as well. Make sure that the service you are looking at has client software or at least instructions on how to set up the service with your iOS devices.
Setting up a VPN service can be done either with a client app or by adding a configuration on your device. For iOS, this is done in Settings > General > VPN > Add VPN Configuration. Likewise, macOS provides a way to add VPN services through System Preferences > Network, then clicking the plus sign ( + ) in the left sidebar to add a new service.
With both operating systems, adding your own configuration may be unnecessary if you’re provided with a proprietary app to make the connection. If you do need to add a VPN configuration, make sure that you get important information from your provider including:
- VPN Type (L2TP, IKEv2, Cisco IPSec, L2TP over IPSec, etc…)
- Server Address
- Account Name
- Authentication Settings
Anti-Malware/Anti-Spyware – Even when you’re using a VPN, the network traffic “outside” of the end points can be vulnerable to malware and spyware. While malware isn’t as much of an issue for macOS and iOS users as it can be for Windows users, you might wish to find a VPN service provider that bundles anti-malware scanner apps with its service. If you choose not to run anti-malware software on your device, make sure that websites you’re visiting (especially if you’re buying something online) are using HTTPS to secure the network traffic between your browser and the remote server. Think of it as an extra added layer of security.
Price – Believe it or not, you can actually get the benefit of a VPN for free, as there are a number of providers who will give you VPN protection without paying a dime…but you’ll still “pay” by viewing ads. Free providers are also more likely to log your activities, restrict exit locations, and not have as much of a commitment to your privacy as subscription VPN providers. However, if you’re just going to need a VPN while on a trip so you can watch your favorite shows, free VPN services may make more sense.
For the best level of privacy, getting a subscription to a VPN service is a better option. Once again, be sure to take all of the factors listed above into account before making your decision.
Can I Create My Own VPN?
 Yes, you can! This is useful if you want secure remote access to your home or small business network or wish to hook up a network between friends for gaming. Apple’s OS X Server app ($19.99) has a bit of a steep learning curve, but it’s possible to set up a VPN service using one of your Macs as a server. There’s also a VPN server/client called Hamachi from LogMeIn that is extremely easy to set up…but there’s no iOS client available. For a private VPN between two Macs, it’s certainly an option.
Yes, you can! This is useful if you want secure remote access to your home or small business network or wish to hook up a network between friends for gaming. Apple’s OS X Server app ($19.99) has a bit of a steep learning curve, but it’s possible to set up a VPN service using one of your Macs as a server. There’s also a VPN server/client called Hamachi from LogMeIn that is extremely easy to set up…but there’s no iOS client available. For a private VPN between two Macs, it’s certainly an option.
OpenVPN provides a way to set up a VPN as a cloud service through Amazon Web Services, and has various client apps available for both macOS and iOS. However, the setup of the service is once again quite onerous.
Regardless of the reason you may use a VPN and what you use to set up your encrypted access, virtual private networks are a great way to keep your data private and protected — especially when using public networks.













Nordvpn, and in my three years experience with different providers I have to say I’m pleased with my decision
Thanks for the post, content was highly helpful and informative.
Have you heard of an outfit called Tec Secure that claims to find attempted intrusions and put encryeption software on your home network remotely, for a fee?
Is it trustworthy?
I can recommend Azire — easy to set up on desktop or mobile device, inexpensive, and extremely reliable. azirevpn.com
Any recommendations on Mac friendly commercial VPN services to choose from? Great article!
Private Internet Access (PrivateInternetAccess.com) is an excellent service. Works with all major platforms, allows you to install and use on up to 5 different computers, and above all it is easy to use – and does what it says it will do. If you purchase a yearly subscription it’s $3.33 per month…
I’ll second PIA VPN! I’ve been using PIA for about two years without issues. My connection is fast, just shy of speeds without a VPN running, this is also something one should consider. PIA is painless, strong, and worth every penny. I pay for mine by the year to save money with the discount.
I have used two or three different ones over the past 2015 years this is the one I use now “airVPN”