![]() First, it was computer viruses, then other forms of malware. Now there’s a new threat out there: stalkerware. If you haven’t heard the term “stalkerware” before, it’s probably because it’s something that has only surfaced in the past few months thanks to an investigative series on Motherboard. In our mission to make you aware of possible threats to your online and personal security, the Rocket Yard wants you to know more about stalkerware.
First, it was computer viruses, then other forms of malware. Now there’s a new threat out there: stalkerware. If you haven’t heard the term “stalkerware” before, it’s probably because it’s something that has only surfaced in the past few months thanks to an investigative series on Motherboard. In our mission to make you aware of possible threats to your online and personal security, the Rocket Yard wants you to know more about stalkerware.
What Is Stalkerware?
Stalkerware is defined as invasive applications running on computers and smartphones that basically send every bit of information about you to another person. This covers the gamut from programs that can be purchased online to give third parties access to basically everything on your computer from photos, text messages and emails to individual keystrokes, to apps that activate your Mac’s webcam without your knowledge.
Who Installs Stalkerware?
Installing stalkerware is a form of domestic abuse, with someone wishing to spy on everything you do for the purpose of making your life miserable.
How Can I Tell If There Is Stalkerware On My Mac or iPhone?
Fortunately, it’s pretty hard for someone to install stalkerware on your computer or smartphone without them having access to it thanks to the built-in security of macOS and iOS. However, like other malware, stalkerware can inadvertently be installed on a Mac by following links sent in emails and social media. Never click on links in emails from unknown senders, and if friends (or former friends…) send unsolicited files, check with that person first or just don’t open it.
If your Mac was “borrowed” by a person for a while and returned with settings or apps that are different than what you remember, it’s time to be investigate. On the Mac, a good way to look for stalkerware is to launch Activity Monitor and look for unknown processes. To launch Activity Monitor, press Command-Spacebar to bring up Spotlight, then type in Activity Monitor and press return. A typical Activity Monitor screen looks something like this screenshot:
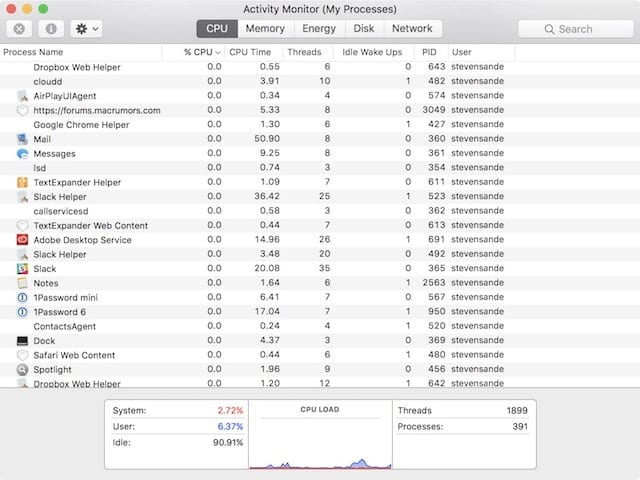
Most of the running processes you see will be related to macOS or running applications, but you might want to check on those that you’re not familiar with. For example, if you think that “mdflagwriter” might be a suspicious process, do a search on the Internet to see what it is — in this case, it’s an operating system daemon (background process) that indexes files, folders and volumes for fast searching. If your search shows that a process could be related to stalkerware, shut the machine down until it can be “wiped clean”.
For iPhones, the monitoring tools are much more difficult to install and often require that the device be jailbroken in order to provide extra system access. If the Cydia app shows up on your iPhone or you find that it’s running an old version of iOS that can’t be updated, your device has possibly been hacked for stalkerware.
Some stalking doesn’t require an app. Let’s say you’ve recently had a bad breakup, and the ex has an idea of what kind of passwords you might use. They can make a “wild guess” at passwords and security questions if they know you quite well, which makes logging into your accounts quite easy so they can see what you’re up to or — even worse — send out messages to others that are allegedly from you.
For Facebook, it’s easy to determine whether your account is being logged into from another location or device. On the Facebook Settings page, go to Security and Login to see when active sessions began (see screenshot below) and log out from them if they appear to be sessions initiated by a stalker.

In many cases, you’ll have a clue that something is amiss as the stalker will often use your email or social media accounts to send out bogus messages. If you feel that someone is doing this to you, the best thing to do is to change passwords on your email and social network accounts, using another computer or smartphone to do so.
Stalkerware Prevention and Removal
In those situations where you think a person may try stalking you electronically, you should not only change passwords and reset your security questions, but enable two-factor authentication as well to make it even more difficult for them to alter your passwords.
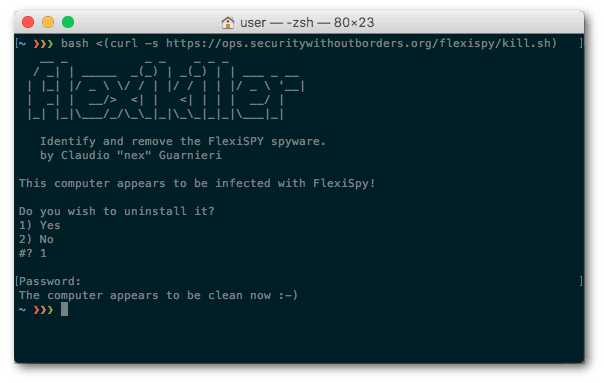
One particularly nasty commercial stalkerware app is known as FlexiSpy. Fortunately, a programmer at the activist group Security Without Borders by the name of Claudio Guarnieri created a tool called FlexiKiller to find and remove the offending stalkerware (see image below):
If a stalker has installed a regular keylogger application (a program that captures all keystrokes on a computer and sends the captured text to a third-party) on your Mac, most commercially available antivirus and security apps will catch known keyloggers.
Jailbroken or suspiciously setup iPhones can be “fixed” by resetting them back to factory condition, then restoring them. Apps that were installed by jailbreaking or by other abnormal means will not be reinstalled. To reset an iPhone or iPad completely, launch the Settings app, then select General > Reset > Erase All Content and Settings. Make sure that you have a backup first!
When you think your iPhone has been tampered with, it’s also good practice to see what apps are installed. This is easy on any iPhone or iOS device — just launch Settings, then scroll down to the list of apps (it begins after the settings for social media). Anything that doesn’t look familiar should be removed from your iPhone.
Earlier I mentioned malware that can be used by a stalker to watch and listen to you without your knowledge. If you’re concerned about such an occurrence as part of an overall stalker attack, I’d highly recommend installing OverSight. It’s a free utility written by security expert and developer Patrick Wardle that notifies users when their built-in webcam or microphone are being activated (see image below).

One last comment: Stalkerware being used against you is nothing to joke about. It can be emotionally and psychologically devastating, so seek out help and support from friends and family. One other excellent resource is the National Domestic Violence Hotline, which can provide both support and suggestions on how to resolve your situation.












there is nothing i can do to remove any app that has been installed on my phone. the apps that installed is listed as system apps. but thank you anyway. i will contenue to look.
I’m pretty sure my boss at work has installed this on our PCs.
What do you recommend for Android phones?
Shut my machine down, you say, until it can be “wiped clean.” I’m sure you’re not talking about a damp rag, but I haven’t a clue about wiping a computer clean, especially without booting it up again. Can you explain?
Keylogger type software has been mentioned for a long time. It has never been mentioned that if( I copy and past the password as I do with 1password), is that a workaround?
Interesting topic and arrticle, but its depth was disappointing. What about the biggest security threat of all, the NSA? How do you propose to detect and counter that? How about a follow-up article in the next issue?
Want to see where your machine’s been going? Check out the latest version of Little Snitch. In addition to monitoring incoming and outgoing connections the latest version can show you what apps reached out to servers across the globe. I’ve been using it for years
Control-spacebar, not Command-spacebar
Nope. Only if you’ve customized the shortcut. It’s definitely Command-Space. Go to System Preferences > Keyboard > Shortcuts and tell me what it says. If it’s showing Control-Space, then click the Restore Defaults button and it will default back to Command-Space.
Steve
You’re both right. CMD-Space is also the default for switching between input sources if you have that functionality enabled. I just checked (I don’t change the defaults, I simply disable those I don’t use).
How Apple missed that oversight is beyond me. I know CMD-Space changes input sources because I’ve been using that key combo to switch between US/Kotoeri (Hiragana/Katakana/Kanji) ever since OS 9.
Thanks for the security info. I was arrested at the Trump rally in Tulsa a year ago because the city police saw me as part of “ liberal media”, which I am. They gave my iPhone to the FBI and they kept it for five months. I wouldn’t use it again. I have it in a Faraday bag. I assume the got everything out of it but I don’t know what they put into it. Don’t know how to cleanse it entirely.