The process of securely wiping a drive, that is, removing every bit of the data it contains and scrambling its content enough to protect the information stored on the drive from prying eyes, is fairly well understood for old-fashioned spinning hard drives. SSDs, on the other hand, can be affected poorly by the same techniques used on hard drives: overwriting data locations multiple times with random data or specific data patterns.
To make matters worse, at least from a security standpoint, even after overwriting data on an SSD, it’s possible that some of the original information is still present on the drive.
Which brings us to the question: Can you securely erase an SSD without damaging the drive, and make sure that all of the information is no longer recoverable?
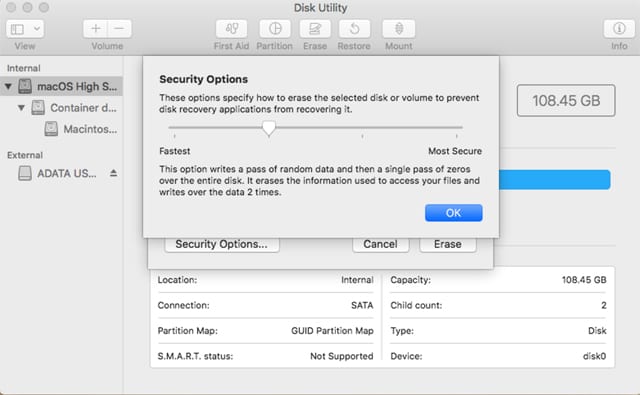
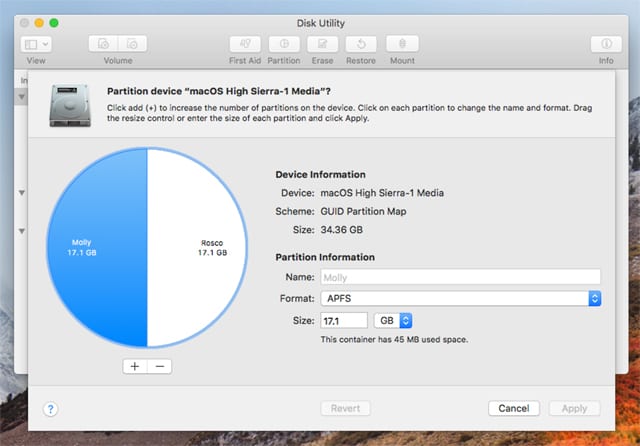
It may be a good idea to review how Disk Utility can be used to erase and protect information in the article: How to Securely Wipe the Data Stored on a Drive in macOS High Sierra.
We originally looked at the changes High Sierra brought to performing a secure wipe. In this Rocket Yard article, we’re going to further explore how to securely wipe an SSD.
SSD Architecture
As we said above, the process of securely wiping a hard drive is fairly well understood. The linear nature of data storage on a spinning drive, along with the ability to access and read, write, and erase data at all active storage locations make the sanitation process pretty easy, though sometimes time-consuming. Essentially, you need to erase the volume and partition maps, and then overwrite each data location using a random or specific data pattern.
The number of times data is written, and the data pattern used for the secure wipe, allows the sanitation process to meet specific security requirements, including those set forth by the DOD or other government agencies.
SSDs, on the other hand, don’t use a linear storage convention, nor are the storage locations directly addressable. Instead, SSDs use a number of mapping layers that hide the physical layout of the flash-based memory, as well as help in managing how flash memory data integrity and lifetime are managed. Collectively, these layers are referred to as the flash translation layer (FTL).
SSDs are also overprovisioned; they contain a bit more flash memory than what they’re rated for. This extra memory is used internally by the FTL as empty data blocks, used when data needs to be rewritten, and as out-of-band sections for use in the logical to physical mapping.
The mapping layers, and how the flash controller manages memory allocation, pretty much ensure that either erasing or performing a conventional hard drive type of secure erase won’t ensure all data is overwritten, or even erased at all.
One example of how data gets left behind intact is due to how data is managed in an SSD. When you edit a document and save the changes, the saved changes don’t overwrite the original data (an in-place update). Instead, SSDs write the new content to an empty data block and then update the logical to physical map to point to the new location. This leaves the space the original data occupied on the SSD marked as free, but the actual data is left intact. In time, the data marked as free will be reclaimed by the SSD’s garbage collection system, but until then, the data could be recovered.
A conventional secure erase, as used with hard drives, is unable to access all of the SSD’s memory location, due to the FTL and how an SSD actually writes data, which could lead to intact data being left behind.
SSD Secure Erase
SSD manufacturers understand the need for an easy way to sanitize an SSD, and most have implemented the ATA command, Secure Erase Unit (used with SATA-based SSDs), or the NVMe command, Format NVM (used with PCIe-based SSDs) as a fast and effective means of securely erasing an SSD.
SSDs that support secure erasing use either a block erase to completely erase the media, including flash memory in the FTL and out-of-band areas; or, if the SSD makes use of encryption built into the controller, the secure erase command will change the internal encryption key, resulting in a crypto-erase, leaving all data encrypted with no means to decipher the encryption; essentially, looking like a collection of random and unrelated data. Some SSDs that have built-in encryption support both full media erase and crypto-erase.
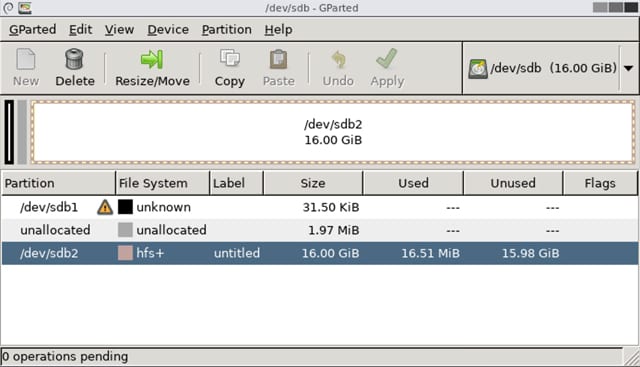
The problem for Mac users is that, for the most part, none of the utilities produced by SSD manufacturers that support Secure Erase Unit, or Format NVM, are able to run natively on a Mac. This leaves us to either create a Live Linux distribution on a flash drive, in order to run a Linux-based SSD utility from the SSD manufacturer (if available), or to use a bootable Windows partitioning and formatting utility that supports the secure erase feature in order to sanitize our SSDs.
Note that not all SSD manufacturers provide utilities that support the secure erase functions. But in addition to the manufacturers SSD utilities (where available), you can also use third-party formatting utilities that support secure erase:
The Encryption Option
As noted above, many SSDs now make use of built-in hardware-based encryption (sometimes called SED or Self Encrypting Drives), which provides a simple method of sanitizing the SSD. Erasing or changing the stored encryption key contained within the SSD will render the content unrecoverable. And as we noted above, there are a number of utilities available that can remove or change the encryption key for you.

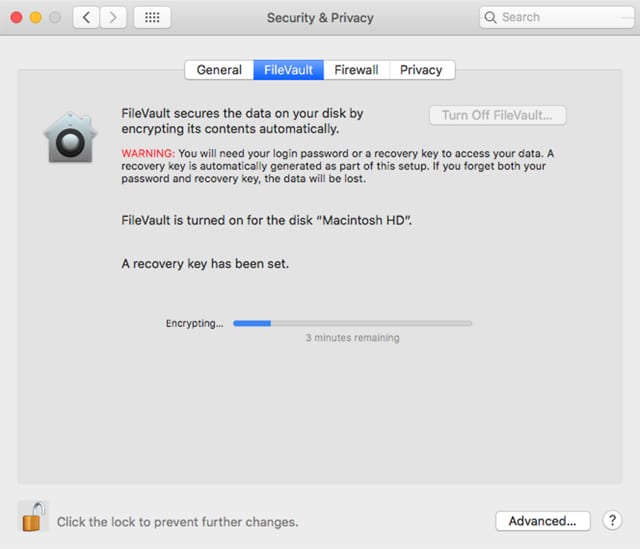
It may seem redundant but using FileVault, the Mac’s full disk encryption system, or the built-in encryption options in APFS, can be one of the easiest ways to help ensure a sanitized drive. The best method is to turn the encryption options on when you first set your Mac up. But if you haven’t been using encryption, you can enable the capability at any time by following the steps outlined in: Data Privacy Day: Keep Your Data Safe From Prying Eyes with FileVault.
With the encryption option on the Mac enabled, you can sanitize the drive by using Disk Utility’s Erase function to perform a basic drive erase, which will include deleting the 256-bit encryption key stored on the volume. Once the key is removed, the data on the media will not be recoverable using conventional recovery software.
To further ensure that the information on the SSD isn’t recoverable using forensic data recovery techniques, you can make use of the secure erase options outlined above to perform a flash memory reset and crypto-erase of the SSD.
Going a Little Further
The last step in securing an SSD is physical destruction of the drive’s controller and flash memory chips. If the SSD made use of built-in encryption, then destroying the controller is all that is needed. The data on the flash memory chips would have been stored in an encrypted state, which could only be decrypted using the embedded encryption key stored on the controller, which was physically destroyed. But, since you have taken the SSD apart to destroy the controller, you may as well drill a few holes through the flash chips, just to make sure.
Wrap Up
SSDs are so fundamentally different from rotational hard drives in how they work that conventional sanitation techniques, such as overwriting data multiple times, just won’t work. But SSDs can still be securely erased; we only need to learn a few new tricks. Chief among these is to start using encryption from the moment you make use of an SSD-equipped Mac.
There’s no real downside to using encryption, and if you’re using a somewhat newer SSD, there’s a good chance the SSD is already making use of built-in encryption to help keep your data secure from prying eyes.
Even if your SSD is self-encrypting, you should also use the Mac’s built-in encryption system, to ensure you have complete control over at least one of the encryption keys used to access the stored information.









I’d like to add any secure erase, weater it be Mac Terminal:diskutil zero disk, or 3rd party utility, both aonly ty and archive the same goal..
SSD’s have garbage collection, which routinely erase the cell(s) evenly,. This is part of the hardware, and usually just by doing zero pass by”software” is useless, as the garbage collection decided when to bank cells..
Thus, to the untrained eye, it “appears” blank, but i do not think you can move any software command to ‘force ‘garbage collection.. In fact and if anythingvusng these software “try” and erase only adds to the decreased write cycle count anyway..
Yes, you are writing a patten of 0’s but its still a write NOT done by the controller itself,
I always use this tool because it’s simple and written in Java so can be used on my personal Mac as well as the Windows workstation at office.
https://www.softpedia.com/get/Security/Secure-cleaning/Shred.shtml
Has anyone tried running ATA Secure Erase from Linux on T2-enabled Macs? I feel like my 2018 MBP SSD slowed down due to heavy disk operations over the years, and would like to perform Secure Erase to restore its factory performance, though I am kind of scared of bricking it, since it’s kind of a different controller architecture.
Fairly certain that while T2 Macs are able to boot into Linux with boot security stuff disabled, last I checked Linux is not able to even see the internal drive. So, I don’t think there is any way to run ATA Secure Erase/Format NVM on a T2 Mac.
That being said, I do not think ATA Secure Erase/Format NVM is even necessary for T2 Macs since all data is always encrypted by the T2 chip. To securely wipe a T2 Mac, I believe the best approach would be to use another Mac with Apple Configurator installed and put the T2 Mac into DFU mode and connect it to the other Mac to restore BridgeOS on its T2 chip, just like restoring an iOS device. I believe this behaves the same as restoring an iOS device and securely erases encryption keys stored in the Secure Enclave, therefore rendering the SSDs data securely erased and unreadable. Read more here: https://mrmacintosh.com/how-to-restore-bridgeos-on-a-t2-mac-how-to-put-a-mac-into-dfu-mode/ and here: https://support.apple.com/en-us/HT208862 and here: https://support.apple.com/guide/security/secure-enclave-overview-sec59b0b31ff
PS. In terms of restoring the SSD to factory default write performance by running ATA Secure Erase/Format NVM, I think you may be out of luck on a T2 Mac.
does this make any sense… in the past, when I have given away hard drives, I would reformat the drive using different file systems. for instance, if the drive is formatted as macOS extended, I’ll do a long format as xFAT, then I’ll reformat the drive with a linux file system. so when the person who gets the drive, seeing that it is a foreign file system, will then reformat it to his preferred file system. I have even made the drive one large linux swap partition. then it is given away. I’ll even change the boot sector from MBR to something else. I do not know if this actually works from a privacy viewpoint, it’s just what I have done in the past. it just seems easier and quicker than overwriting data 14000 times.
No. Writing a new file system to the media only writes a blank directory and block allocation tables. The file data remains, you only remove easy means of finding the data. To erase one needs to overwrite all blocks in the drive which an SSD is smart enough to defeat. Way back when, formatting a floppy disk did write the entire surface including laying down the markers for start of sectors.
Long ago when I was custodian of classified automated data processing equipment we were not allowed to “clear” ATA drives to release from our controlled environment because we knew the drive kept spare blocks out of our reach, used as automatic replacements for weak or error blocks. SCSI allowed us to monitor the bad block list. When new drive came in first thing we printed the list of bad blocks and the grown bad block list. When the drive left our hands those lists must be unchanged. Else the drive went to the classified crusher.
I have more of a question, rather than a comment..
Does resetting the disc as a partition erase securely, for a reinstall of the OS, etc… ?
I use the Soft Raid software for the SSD’s in my external bay, to erase and initialize the drives…
I have had trouble trying to use the Disk Utility on the raid
Since when does Gparted support secure erase? Not really usefull..
If you have a newer mac where the ‘ssd’ is in fact soldered to the motherboard then you really have to use filevault and/ or a third party tool to erase your data before selling on your machine! Physical drive destruction is not an option.
I had problems encrypting my external HDD backups using AFPS encryption when initializing them. The HDDs would encrypt but they became very unreliable and eventually, I had to restore them to MacOS Extended (Journaled) state. If I want to use Filevault, it takes over a week to do so (they are 2GB HDDs) which is very time consuming. Is there another way to achieve this using an external app?
Very useful description of the situation – I’m goiing to change my strategy because of what I learned. (Programmer since 1970, Mac user since 1984)
But what about the far more common need to securely erase just one file?
To erase the whole disk, what happens if you move it to another machine which will not recognize the crypto and want to reformat the drive?
The best and simplest sanitation technique for any kind of disk is:
1. Erase disk so that all capacity is shown as free.
2. Duplicate a large monolithic file ¡(to speed up process), like movie to fill disk. Continue with smaller files until 0 kb is left.
3. Erase disk to show all as free space (optional).
Is there an application to do it on Mac? Thanks.
COMPLETELY AGREE. That is the method I always use, even when Disk Utility did have the option to “securely erase” the drive. I would completely overwrite the drive to capacity, THEN “securely erase” it… Just to be sure.
Back in 1988 when I was taking a Compiler Design class, I wrote a program that filled the disk. I guess I should say that I wrote a program that had a bug in it that resulted in a full disk!