Today, I am going to write about trends in Mac threats. But first, I want to provide some data. Mac malware detections are gaining on Windows. In 2019, Macs were infected almost two times more than Windows. Mac malware detections overall for 2019 were about four times higher than for 2018.
So, we see a significant rise in Mac threats. It is not unexpected, though. The Mac market share is becoming more significant, so it is obviously becoming a bigger target for attackers.
The top 10 threats on the Mac make up about 84% of the total. All 10 of these are PUPs (Potentially Unwanted Programs) and adware like Search Marquis. None of this is the truly malicious stuff – the stuff that is trying to steal your data or do keylogging, etc.
Notable Mac Malware
Let us take a look at some of the notable malware threats that experts have seen so far in 2020.
1. ThiefQuest
The first one of these threats is called ThiefQuest (originally called EvilQuest). This malware was spread via torrents and through modified copies of legitimate apps.
At first, security experts believed that ThiefQuest was ransomware. There were some good reasons for that. It started encrypting files when you installed it. It also dropped a ransom note. However, as researchers dug in a little deeper, they saw some things that were not consistent with ransomware.
For example, everyone infected with this malware received the same ransom note with the same Bitcoin address. That is not normal for ransomware. It means that if somebody sends a payment to that BTC address, there is no way for the cybercriminals to know who sent the payment. On top of that, there was no email address in the ransom note. So, there was no way to contact the malware authors and tell them that you have paid and request your decryption key. All these factors looked suspicious.
Another interesting thing was that the encryption key was written in plain text at the end of the encrypted files. If somebody got infected and had their files encrypted and had no backups, there was a way to decrypt those files.
Later, it was found that ThiefQuest was actually exfiltrating an exceptionally large amount of data from the system. All the ransomware activity turned to be fake. It was just a distraction. Hackers wanted to keep their victims looking at many ransomware bells and whistles rather than learning that this malware collected data from the system.
ThiefQuest was exfiltrating data from the user folder via HTTP sequentially picking files with certain extensions and sending them up to the hacker-controlled server. It also did some other interesting things like keylogging and viral infection of other binaries in the user folder – for example, Google Chrome update files.
2. Bird Miner
Another piece of malware is called Bird Miner. This one is a crypto miner. It is designed to mine the cryptocurrency called Monero. Bird Miner was distributed through piracy of a large number of audio apps. A lot of these apps were available through the VST (Virtual Studio Technology) crack site.
This malware worked by installing a virtual machine program called Qemu. This emulator would run a tiny Linux shell system with the open-source XMRig Monero miner. It was difficult to find what this malware was doing.
3. Lazarus group
This year, the North Korean hacking group known as Lazarus, has been actively distributing plenty of new malware pieces. These are FallChill, GMERA, Dacls RAT, and many more.
Lazarus malware samples typically come in the form of either legitimate Trojanized apps or fake apps that are Trojanized. A lot of them come in the form of stock trading apps or cryptocurrency apps. Some of them are open-source apps that have been modified. Others are just fabricated completely.
Some of the early versions used malicious Word documents that would have a malicious macro that managed to escape the sandbox and install files on the system.
Nasty Adware tricks
Let us move to adware, as this is really interesting. Malware on macOS, a lot of times, is kind of lame. It is not very sophisticated, and it is pretty simple. However, Mac adware has recently become more complex.
1. Modifying a copy of Safari
For getting installed, some adware would modify a copy of Safari. This malware would obscure the whole screen and hide all your desktop icons and windows that are open. And while this happens in the background, it makes a copy of Safari. It modifies several JavaScript files found inside the app bundle and then launches that modified copy of Safari while deleting the original app.
If you wanted to open the legitimate version of Safari again, you would find that some settings were changed. You would most notably find that a Safari browser extension had been activated without you having to click any buttons. Normally, if you wanted to install a Safari browser extension, an alert would come up that you had to click and allow it to run.
Users had questions like: “Why did macOS let it run? Wouldn’t that break the code signature?” Yes, technically, it breaks the code signature. But because that copy of Safari was not quarantined—in other words, it had not been downloaded from the Internet—macOS was perfectly happy to open it up without checking the code signature.
2. Malicious profiles
Adware used other cunning tricks like installing malicious profiles. These are system configuration profiles that you might push down from an MDM like Jamf. But in this case, they are installed with the profile’s command-line utility. These profiles have a couple of goals. Their goals are to lock down the Safari and/or Chrome homepages and the search settings.
Once these profiles are installed, you find that in Safari and Chrome, you can no longer change your homepage or set a new default search engine. That is because these are now considered to be managed by your admin, even though this was not deployed via an MDM.
Unfortunately, Apple has no API for managing this, so antivirus software cannot safely remove these profiles. If you see these profiles, they need to be removed from the system.
3. Managed preferences
Another hacker technique has to do with managed preferences. In this case, your browser becomes managed very similar to what happens with the system configuration profiles, but not quite exactly in the same way.
Most of the time, these managed settings can be changed by the user within Safari or Chrome. The files responsible for setting these preferences are found in the Library > Managed Preferences folder.
If you see different things in that folder and you, as an admin, did not put them there, they need to be deleted.
4. Changes to sudoers files
Adware started to make a lot of sudoers file changes. As you probably know, the sudoers file determines who can get root permissions. So, a non-admin user should never be in the sudoers file. Admin users, typically, are found in the sudoers file, but they should not have certain kinds of access.
What adware has been doing is making one or two changes to the sudoers file to allow continued sudoers access without a password. It sets a no-password requirement for a particular process, so that process can use sudo all at once without a password, running under this particular user.
Other malware types approach this in a slightly different way. They let all processes running under the user execute sudo with no password requirement whatsoever. These changes create a vulnerability that can be taken advantage of in the future by other malware writers. That means that if I were a malware author and infected the system, I have zero work to do. I can get root permissions and do whatever I want – all without a password.
If you see these changes in a sudoer’s file, you definitely want to fix that.
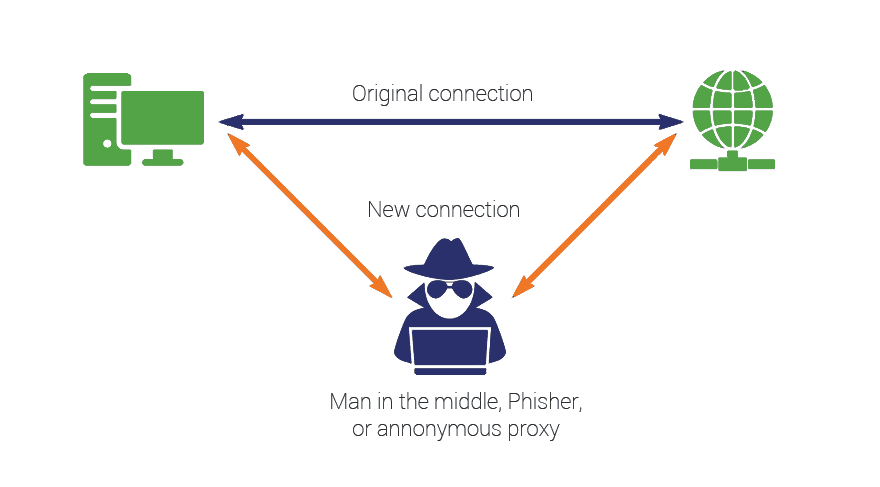
5. Man-in-the-middle attacks
MITM attacks behave something like a virus. Obviously, a lot of malware strains do this. Hackers use this technique to grab your network data. It is a very handy way for malware to hoover up a whole bunch of data on all your web browsing, all your network traffic, and get a lot of very sensitive information.
Adware authors use this method not to suck up all that data but to inject data into the stream, to inject ads into your HTTP and HTTPS traffic.
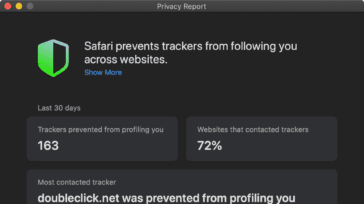
One of the most common programs used in such operations is an open-source program called mitmproxy. It is designed to allow web development admins to debug their code and see what is going on. Adware authors are using mitmproxy to inject ads. They are also installing a trusted profile for mitmproxy to inject data into the HTTPS traffic, not just the unencrypted HTTP traffic.
If antivirus tools detect and remove mitmproxy (when it is installed maliciously), which needs to be done to protect the user, it, unfortunately, causes a loss of network connectivity. And in these cases, you still must go into the network proxy settings and remove all the settings for those proxies that were set up. You also definitely want to look for any unwanted certificates in the keychain that will give the attacker the ability to snoop on your encrypted traffic.
6. Data collection
Many adware types these days are doing a lot of data collection. It is a different kind of data collection than malware does. Malware is looking for private documents, passwords, and certificates that may be used to gain access to a system through SSH or something like that.
Adware collects a quite different kind of data, but it is still not data you want to be out there. It collects things like the computer’s unique identifier, IP address, username, macOS version, Safari version, etc.
With some adware species, it gets worse. Adware can create and send to its author the list of everything you have installed on the system, including applications in the Applications folder, installed launch agents and daemons, installed system configuration profiles, etc.
Some adware can do proxying with the possibility of either intentional or accidental exfiltration of your network data. So, even though adware is something that many people think is only a nuisance, it is still something that you really do not want on your computer – it can lead to dangerous vulnerabilities being opened up.
Conclusion
Let me sum up everything.
First of all, we know that Mac malware is on the rise, and I believe that this is partly due to the Mac’s rising market share. It is also likely to be prompted by who uses Macs. If you look at Windows machines, there are a lot of really cheap ones out there. Are the people buying these really good targets? Maybe yes, maybe no. On the other hand, if somebody is buying a $3,000 Mac, are they a good target? Pretty definitely, yes.
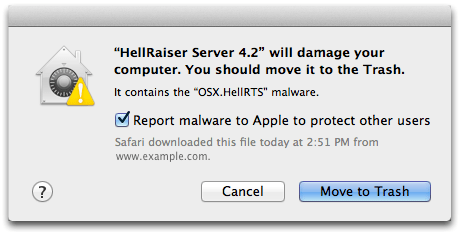
I expect Mac malware to continue to increase over the next few years and into the future. We have seen that Apple has been doing many things to combat malware with each version of the system.
Unfortunately, Apple’s steps are not always successful. For example, in response to putting more requirements on notarization and code signing, we see a lot of malware coming these days, “un-code signed.” Rather than signing, hackers just walk the user through the process of how to open an unsigned app.
We see that although malware is rare, it can really be nasty. For example, ThiefQuest can grab a lot of data and do a lot of damage to the system.
Further, many times, malware can stay hidden for years; for example, Fruitfly was discovered in 2017. It could access the webcam, the microphone and create things like child pornography. Fruitfly had been in the wild undetected for more than ten years!
And finally, adware can actually be just as sneaky and malicious, if not more so, than Mac malware. Adware is doing all kinds of things. It can access data, use vulnerabilities to get installed and cause vulnerabilities after it gets installed. Even though adware is generally thought of as less dangerous, you really do not want it on your systems.















thank you for sharing all this info. great article always a good thing to stay in the know of current threats etc.
i do have a thought/question/or whatever the best term might be that eludes my fingers.
while reading this artticle i had this sentiment that ive found myself arriving at many times prior to this, which always happens when i read articles about the current security threat articles. and it always crosses my mind and thus causes a bit of frustration as its something that is a recurring theme or issue that could be something of a internal blockage in my brain, or its actually something that isnt in my head and is due to either accidental oversight, or purposefully omitted which i cant exactly fathom the latter of two as to why it would be
and the recurring issue i have, is that every security based article for focus of this post, where the article describes a new threat and where to find it, and what all types of haneous stuff it is able to do, then the where it came from, how it was delivered. etc etc
theres always one thing seemingly missing, which imo is like the thing that should nver not be omitted or left out
and tjhat is “what the badware that was in the package, looks like< or rather how to prpoerly identify the items that id just read need to be removed if found, be a bad certificiate, a pkg file, a plist, or any other type of file type or content.
its thesame thing as getting a package in the mail and you open it, and theres a bill of lading, a packing slip, instructions, but no info anywhere inside or outside on the box that gives you information that tells you what the item(badware) in the package looks like, so we can know when we see it, that its the one that needs to be removed, etc.
this is something that ive encountered on every adware malware antivirus app/programs website, and reading an artifcle from them too many times to care to count,
im like ok i know what i need to use to search for it, where it should be found, and how dangerous it is, and what to do if its found BUT WHAT AM I LOOKING FOR,
the certificate thing is what per se triggered this, i have no clue about which certs should of shouldnt be installed or in place,
ill clarify
I dont have a clue as to where to even start on criteria to use when searching through the titles of all the certificates or websites or daomains that should or shouldnt be present, that would signal to me that i bneed to remove which ever ones one it is,
ive tried to attempt to read through all the domainsa, or sites that are listed in the settings menu,
theres no given definitive list of specific names of apps or folders or etc that the badware has been found to be in or from , so as informative as this is and helpful, without proper criteria to be able to accurately id the offending item, all these articles are in a crude sense if i may is or can be seen as fodder that just causes panic or uneasyness or just isnt actually truly helpful
idk im probably blindly missing something seeeminglyu too obvious to not miss or there are unsaid spoken reasons im not privy to as to why this is
its a genereal rant or frustration and not intended to be specific to this instance
Quite informative. Thanks.
Good to know. Any useful tips on how to protect against some or all of these?
Hi smayer97!
The rule of thumb is to follow safe software installation practices. You should never install apps from unofficial app stores not controlled by Apple. Treat freeware installers like Bundlore with caution and always check them for extra items that could be hidden in plain sight. To be able to do bad things, current Mac malware requires users to perform some actions – grant rights. So, be careful with allowing any app to access your data, change settings, etc. Add an extra security layer to your Apple ID and other accounts by enabling two-factor authentication (2FA). Use the newest version of macOS or iOS your device can run. One more wise move is to make backups. iCloud or ordinary flash drives will help you not lose your data in case of a system glitch or malware attack.
Thx for the heads up!
–How about other app-stores or repositories like Sourceforge, Softonic or CNET??
..and how about antivirus-software, any recommendations?
1) I wouldn’t recommend alternative app stores as they may have not such resources as Apple to protect their repository.
2) Apple environment does not allow apps to interfere, so antiviruses are not so important here. There are a lot of good reviews of Malwarebytes.